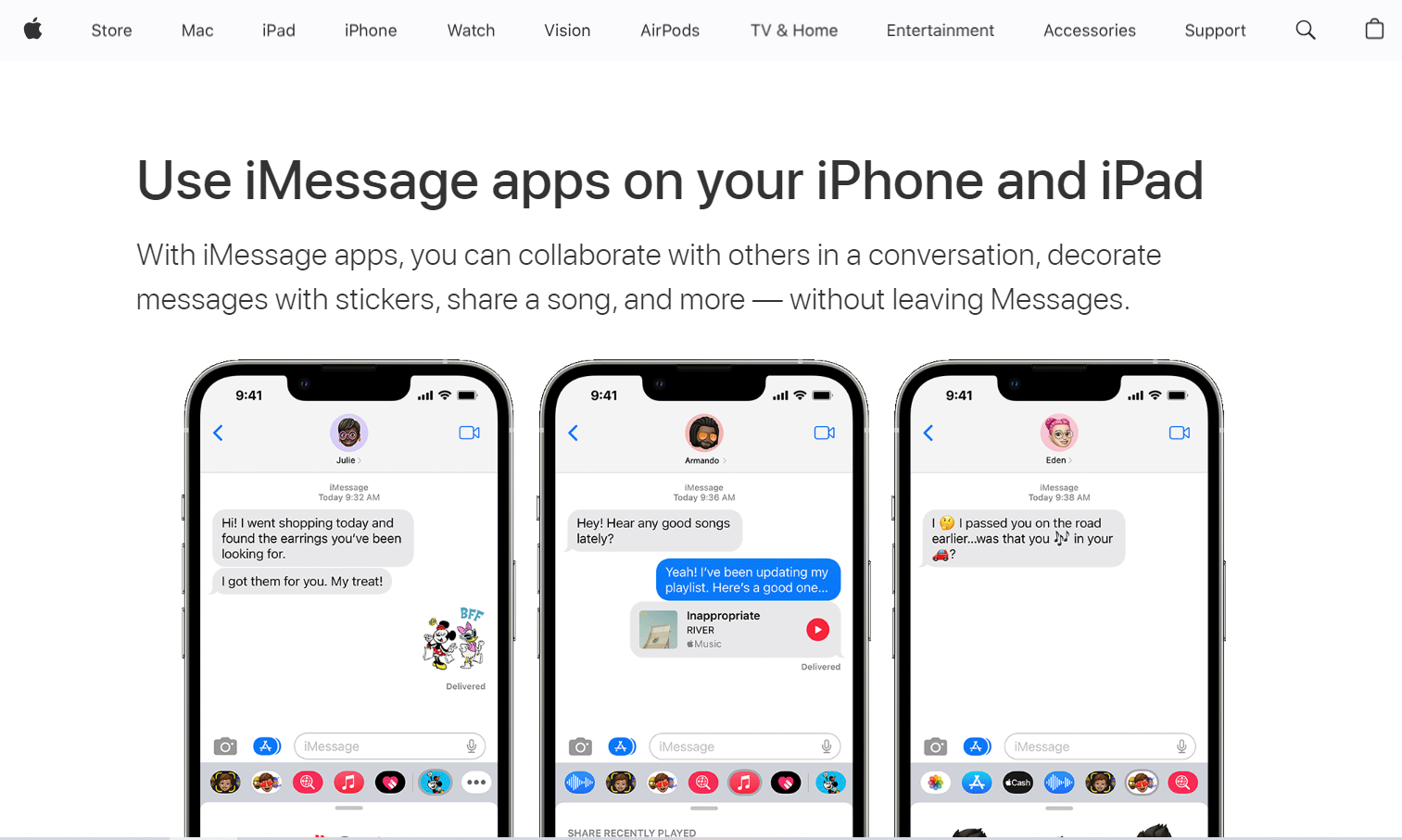
iMessage, Apple’s proprietary messaging service, is the messaging platform of choice for iOS devices. It’s known for its security and user-friendly features, making it a popular alternative to other messaging apps. However, healthcare workers should first ask if these security features are enough to help establish and maintain compliance with the Health Insurance Portability and Accountability Act (HIPAA).
The answer to the question “Is Apple iMessage HIPAA-compliant?” will help determine if it’s indeed okay to use it for sending and receiving healthcare messages.
Table of Contents

iMessage and HIPAA Compliance Challenges
Despite its security features, iMessage faces the following challenges in achieving full HIPAA compliance:
Lack of Business Associate Agreement (BAA)
HIPAA requires entities handling protected health information (PHI) to sign Business Associate Agreements (BAAs). Currently, Apple does not sign BAAs for its consumer-focused services, including iMessage, which poses a hurdle for healthcare providers aiming for compliance.
Non-compliant data storage and backups
Apple’s servers temporarily cache message data for 30 days. This allows users to retrieve messages despite being offline. The iMessage developer will permanently delete all cached data after this period.
However, iMessage’s storage and backup processes raise concerns. Users have the option to turn on iCloud for data backup. Therefore, message compliance also requires iCloud compliance. But iCloud is not HIPAA-compliant. In fact, iCloud’s Terms and Conditions state:
If you are a covered entity, business associate, or representative of a covered entity or business associate (as those terms are defined at 45 CFR § 160.103), You agree that you will not use any component, function or other facility of iCloud to create, receive, maintain or transmit any “protected health information” (as such term is defined at 45 CFR § 160.103) or use iCloud in any manner that would make Apple (or any Apple Subsidiary) your or any third party’s business associate.
Is iMessage HIPAA-Compliant?
No, iMessage is not HIPAA compliant. Despite its strong security measures, Apple’s proprietary instant messaging app excludes important HIPAA features: the business associate agreement and HIPAA-compliant data backup. Given the current state of iMessage compliance, healthcare professionals and other covered entities should exercise caution when using it for patient-related communication.
Apple does not provide a BAA for covered entities and their business associates using iMessage, which is required under HIPAA law. If healthcare data containing PHI resides in Apple’s servers temporarily, then that’ll make the company a business associate of a covered entity. The thing is, Apple will not sign a BAA, which disqualifies iMessage as a HIPAA-compliant solution. Moreover, its data storage, iCloud, cannot be used to handle any protected health information.
If you’re looking for HIPAA-compliant instant messaging services, consider looking for alternative solutions like OhMD and Trillian.

What Are iMessage’s Security Features?
iMessage can be considered a secure messaging platform, provided you do not use it to handle PHI. Let’s break down the much-touted security features of iMessage, which you can review on Apple Platform Security:
- Encryption: iMessage offers end-to-end encryption, transmitting messages securely so only the intended recipient can decipher them. Outgoing messages are individually encrypted for each recipient’s device using a combination of HMAC-HA256 and AES in Counter (CTR) Mode. The message key is encrypted using RSA-OAEP or Elliptic Curve Integrated Encryption Scheme (ECIES), depending on the iOS version.
- User authentication: Apple links messages sent through iMessage with specific Apple IDs. Only authorized individuals can access the messages. In addition, the company employs additional security measures in its devices, such as Face ID and Touch ID.
- Digital signature: Messages include a digital signature using the Elliptic Curve Digital Signature Algorithm (ECDSA) to verify the integrity of the decrypted plaintext.
- Dispatch to APNs: Encrypted messages are sent to Apple Push Notification Service (APNs) for delivery. While metadata isn’t encrypted, communication with APNs is secured using a forward-secret TLS channel.
- Attachment handling: Attachments exceeding APNs’ size limits are encrypted using AES-CTR with a 256-bit key and uploaded to iCloud. The recipient receives an iMessage containing the encrypted attachment’s key, a Uniform Resource Identifier (URI), and an SHA-1 hash for confidentiality and integrity protection.
- Group conversations: For group conversations, the encryption process is repeated for each recipient and their devices.
- Message storage: Messages are stored on Apple servers for up to 30 days, enabling delivery to offline devices. The deletion from APNs upon delivery and queuing for offline devices distinguishes iMessage from typical push notifications.
- Sharing names and photos: When users share their name and photo, the record key is encrypted and sent via iMessage. The recipient retrieves the encrypted record from the CloudKit database, decrypts it, and verifies the signature for authenticity.
Using Secure Messaging for Healthcare Communication
Unfortunately, there’s no guarantee of iMessage HIPAA compliance. Covered entities cannot use the Apple-owned instant messaging app to create, transmit, receive, or store any messages that include protected health information, such as patient names, addresses, fax numbers, medical record numbers, and more.
In addition to exploring secure messaging options, healthcare providers are increasingly turning to fax broadcast systems for mass communication needs. These systems offer a secure and efficient way to send information to multiple recipients while maintaining compliance with HIPAA standards. They are particularly useful for distributing general healthcare information, alerts, or updates to a large group of patients or colleagues.
To ensure HIPAA compliance, healthcare practitioners should look for alternative platforms designed explicitly for telehealth and telemedicine communications. With HIPAA-compliant messaging services, you can confidently communicate with patients and colleagues without compromising patient privacy.







