July 24, 2023
Over the Memorial Day weekend, a cyber threat actor began exploiting a zero-day vulnerability in the MOVEit file transfer service (CVE-2023-34362).
On May 31, 2023, an advisory on the vulnerability scale was issued by Progress Software, which quickly released patches to fix the bug. Investigations regarding the cyber exploitation revealed unauthorized access to customer data within the MOVEit server database.
Ipswitch, a US-based Progress Software Corporation subsidiary, developed the managed file transfer (MFT) solution commonly known as MOVEit Transfer. Accordingly, companies use the MOVEit file transfer service to transfer files to their customers through SFTP, SCP, and HTTP-based uploads. Customers can manage the Progress MOVEit Transfer while the developer controls the cloud SaaS platform.
Table of Contents
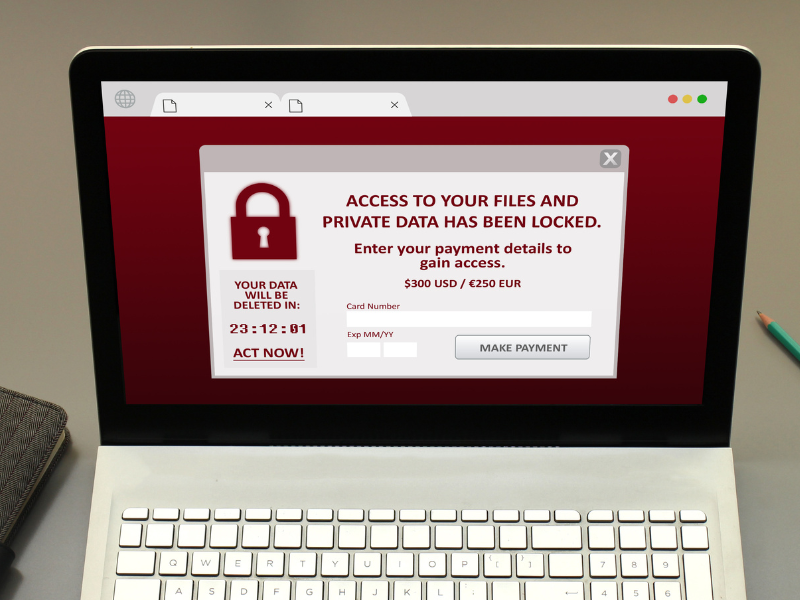
Demands and Countdown to Payment Deadline
Following reports of unauthorized access within the MOVEit server database, the Clop ransomware gang said they were liable for the attacks just a week after the news broke out. They also confirmed the issuance of ransom demands alongside threats in exchange for stolen data. The affected firms were only given until June 14 to pay the ransom money or get their confidential information exposed.
Zero-Day Vulnerability Exploited in MOVEit File Transfer Service
Since the incident last May, the file transfer service has been jeopardizing more than 300 organizations and causing more damage than cyber experts can imagine. According to the reports, hackers have been actively exploiting a zero-day vulnerability in the MOVEit Transfer file transfer software to steal data from organizations.

Major Companies Impacted by MOVEit Attacks
A few days after the detection of the attack, various large companies and enterprises confirmed that they were affected, including the airlines British Airways, the University of Rochester in New York, Aer Lingus, the UK drugstore chain Boots, and the Nova Scotia provincial government. The MOVEit attacks successfully stole data from more than 300 organizations. Several companies also said their targeted applications were infected with a web shell known as LEMURLOOT.
The majority of the stolen data from these companies came from their payroll and HR service provider, Zellis. While the impact’s severity remains unclear, Nova Scotia Health already confirmed that around 100,000 of their employees were affected.
Clop Ransomware Group and FIN11 Suspected of Involvement
According to reports, the Clop group was not alone in doing these cyberattacks. The Clop ransomware group involvement was associated with the FIN11 threat group. These groups actively exploited the MOVEit vulnerability in file transfer service on the Accellion FTA and GoAnywhere MFT. Aside from using ransomware, these attacks also involved data theft and exploitation.
More companies attributed the attacks to the Clop group and FIN11, including Microsoft and Mandiant. According to Microsoft, there are also other affiliates from Clop, like Lace Tempest. Meanwhile, Mandiant said the attacks were connected to a new threat cluster called UNC4857. Accordingly, more than 2,500 instances of MOVEit software are exposed based on the Shodan scans. On the other hand, Censys reported that over 3,000 hosts running the service were at risk.
Meanwhile, other reports said that Clop may have been planning the attack for almost two years. As early as July 2021, the Cybersecurity firm GreyNoise found evidence indicating that Clop was already testing ways to exploit the zero-day vulnerability. Accordingly, the Clop group planned a massive-scale attack as they had the available automation tools to steal vast volumes of data from large companies.
In response, the US Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) showed a joint security advisory to minimize the effects of Clop exploits. The Health Sector Cybersecurity Coordination Center (HC3) also warned about potential vulnerabilities in health and public health sectors.
Ransom demands and data exposure threats
Many companies have resurfaced and claimed they were affected by the MOVEit attacks. The Clop ransomware gang took this opportunity to collect ransom demands from large enterprises with stolen data. They have set a deadline of paying the ransom money until June 14. If they move past the deadline, they could risk exposing their data.
While the impact of MOVEit attacks on companies has yet to be determined, the scale of the attacks should become more apparent from June 14. However, it may take several weeks or months to get the whole picture of the exploitation.

Mitigating the MOVEit Vulnerability
Third-party breaches like MOVEit vulnerability pose serious security risks that can disrupt businesses and healthcare organizations. Regular risk assessment can help mitigate the harmful effects of these data breaches in your organization.
Here are some ways to mitigate these types of risks:
Conduct specific risk assessments
A centralized vendor inventory is vital to identify which third-party vendor relationships use MOVEit. Once you have a list of third-party vendors, you can start doing risk assessments to resolve security gaps.
Monitor the impacted vendors
Be vigilant not only for the risks of the MOVEit attack but also for other potential data breaches. Regularly monitor suspicious activities and update all systems with the latest security patches.
Create a robust incident response plan
In a cybersecurity attack, an incident response plan is crucial to mitigate potential damages. It also outlines the protocols you, your IT team, and stakeholders should follow in case of a security breach.