Prioritizing the security of your Kubernetes cluster and Kubernetes tools for HIPAA compliance is vital. For one, it helps safeguard your organization against security breaches, reducing the risk of data leaks.
Compliance holds exceptional importance, particularly in regulated industries. It also requires development and IT operations teams to have clearly defined responsibilities and roles and employ tools and practices encompassing security frameworks, policies, and API server monitoring.
Table of Contents

Understanding HIPAA Compliance in Kubernetes
The healthcare industry is increasingly adopting Software-as-a-Service (SaaS) and cloud applications. These cloud platforms allow organizations to leverage automation, artificial intelligence (AI), business analytics, and enterprise-wide data access to drive innovation and optimization across various healthcare tasks.
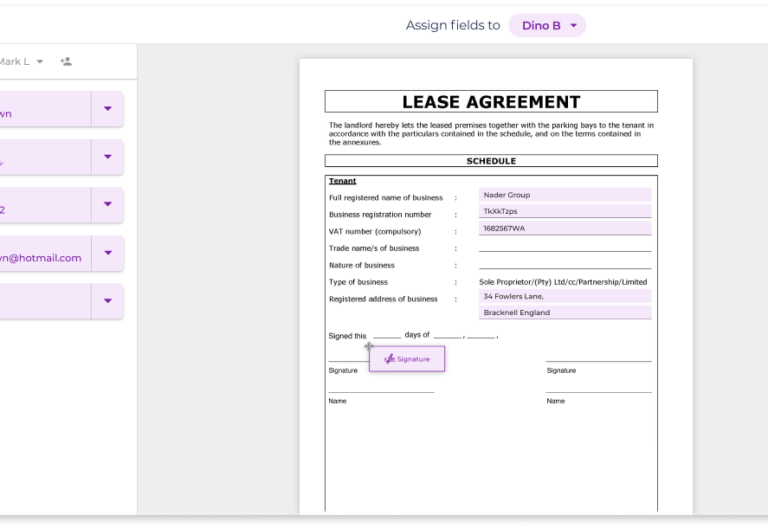
Consequently, developers are turning to services like Kubernetes to build scalable healthcare applications. While the open-source system provides numerous benefits for developers and healthcare users, it is crucial to ensure that containerized applications comply with HIPAA regulations.
Here are some steps you can take or consider to ensure HIPAA compliance in Kubernetes systems:
- Understanding your data: As containerized apps handle data internally and externally, it is essential to have a clear understanding of where the data resides, its movement, and who has access to it. A properly configured Kubernetes system can support data orchestration in a compliant manner.
- Configuring access controls: Each container should adhere to the principle of least privilege and, when applicable, adopt a zero-trust architecture. Fine-grained access controls, such as Role-Based Access Control (RBAC), can ensure that only authorized healthcare providers can access patient data.
- Encrypting data: Kubernetes, equipped with the appropriate modules, enables data and container encryption through at-rest encryption mechanisms. Since HIPAA mandates encryption for all patient data, having encrypted containers for applications handling patient information is essential for compliance.
- Backup of containers: Consistent systems backups, including containers, are required for HIPAA compliance. By putting in place an automatic backup system, it ensures that the storage media containing patient data are sufficiently backed up.
- Implementing scanning: To prevent vulnerabilities, scanning container systems that deal with patient data is advisable. Regular scanning identifies possible security holes and enables quick fixes.
These actions can help healthcare firms improve the HIPAA compliance of their containerized applications built on Kubernetes, assuring the safe handling of sensitive patient data.

Tools for Kubernetes Compliance Under HIPAA
Several tools are available to assist organizations in achieving Kubernetes compliance under HIPAA.
Here are some of the most popular tools:
- Open Policy Agent (OPA): OPA is an open-source policy engine that enforces security policies in Kubernetes. It allows for defining guidelines for various aspects like access control, resource limits, and network security.
- Kubescape: Kubescape is a security scanner designed to identify Kubernetes clusters’ vulnerabilities. It scans Kubernetes manifests, images, and pods to uncover potential vulnerabilities.
- Trivy: Trivy is another security scanner that helps identifies vulnerabilities within Kubernetes clusters. It scans images and pods to detect any known vulnerabilities that may pose a risk to the system.
- Calico: Calico provides a network security solution for Kubernetes. It enables the enforcement of network policies, including firewall rules and access control lists, to protect communication within the Kubernetes environment.
- Istio: Istio is a service mesh solution for Kubernetes. It provides control over traffic between microservices in a Kubernetes cluster. Istio can also enforce security policies like access control and encryption to enhance the system’s overall security.
By leveraging these tools, organizations can enhance their Kubernetes security posture and ensure compliance with HIPAA regulations. These tools assist in enforcing policies, identifying vulnerabilities, and securing network communication within Kubernetes clusters.

Best Practices for Achieving HIPAA Compliance in Kubernetes
Maintaining compliance with HIPAA regulations in Kubernetes is essential to employ secure technologies and adhere to configuration guidelines. It is also necessary to help handle secrets separately from images, encrypt data upon storage, and ensure that all PHI transmissions over the Kubernetes network are encrypted.
Below are some best practices that can further help achieve compliance:
- Utilizing a secure connection when pushing to or pulling from the registry
- Ensuring that the container incorporates the latest release of the image
- Implementing network traffic segmentation to enhance security
- Adhering to container runtime configuration standards, such as those outlined in the Center for Internet Security (CIS) benchmarks
- Identifying potential breaches at both the infrastructure and container levels, utilizing a container-specific operating system
- Configuring containers to operate with the minimum necessary permissions
In general, organizations should make use of trusted content delivery networks (CDNs) and verified cloud storage services to maintain image integrity and authenticity at every stage of the image life cycle, starting from creation and extending to deployment.